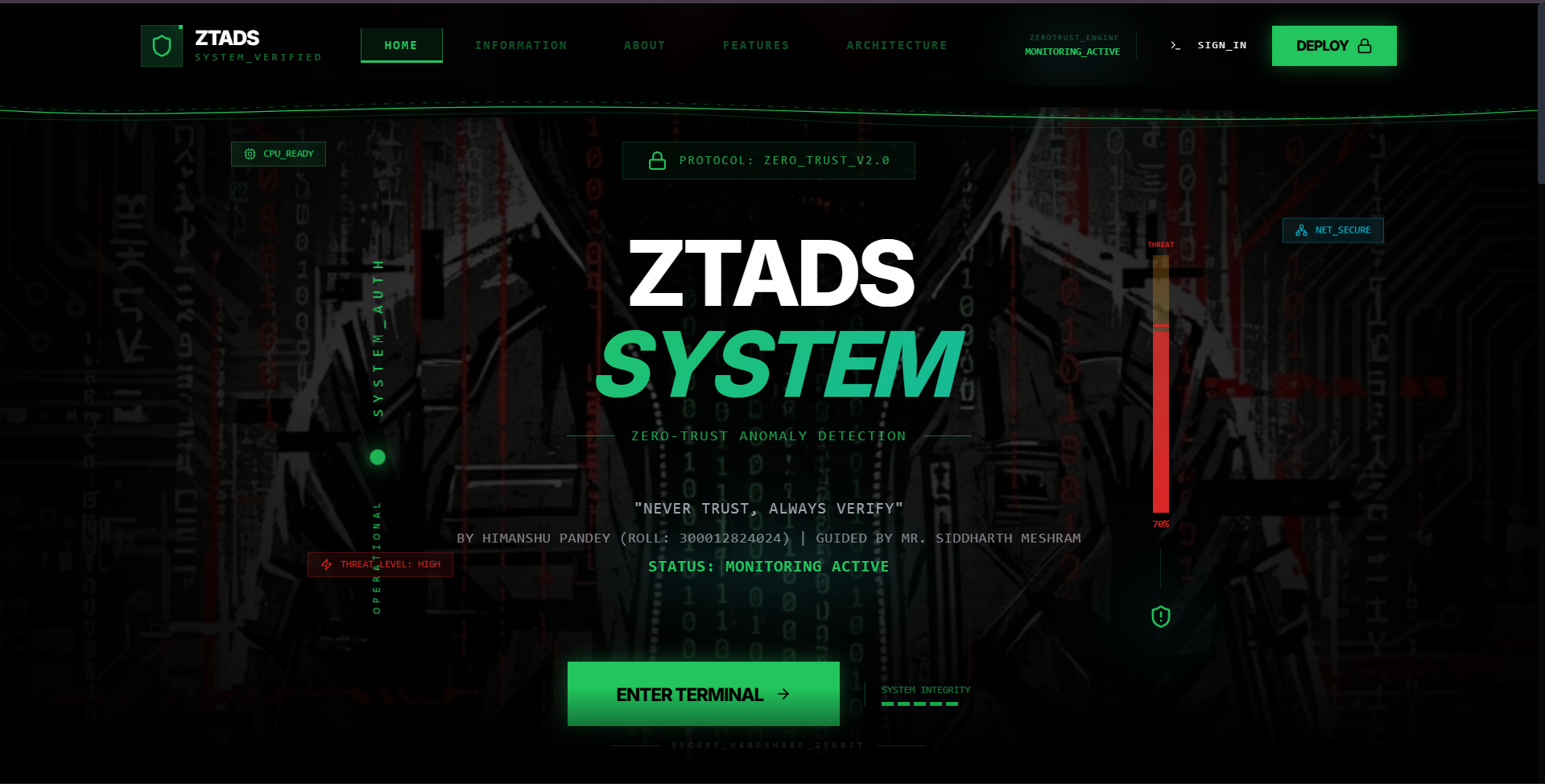
ZTADS — Zero-Trust Anomaly Detection System
A zero-trust anomaly detection system designed to monitor and secure network traffic using machine learning to identify threats in real-time.
Visit websiteThe Problem
Traditional perimeter-based security models assume that everything inside a network can be trusted. This assumption breaks down quickly in modern environments with remote work, cloud infrastructure, and increasingly sophisticated attackers who can move laterally once inside.
ZTADS was built to address this by enforcing a zero-trust posture — every packet, every session, and every user is treated as potentially hostile until verified, continuously monitored for anomalous behaviour.
How It Works
The system captures live network traffic and passes it through a pre-trained machine learning pipeline trained on the CICIDS-2017 dataset. Feature extraction — including flow duration, packet lengths, inter-arrival times, and flag counts — feeds into a Random Forest classifier that flags anomalous traffic in under 100ms.
Flagged sessions are logged to a SQLite database and surfaced through a real-time Flask dashboard, where analysts can review alerts, inspect packet payloads, and trigger automated responses such as IP blocking via iptables.
Key Features
Real-time traffic capture using Scapy and libpcap, paired with a live anomaly feed. The zero-trust engine evaluates every connection against a continuously updated behavioural baseline, raising alerts when deviations exceed a configurable threshold.
The ML model achieves 97.4% accuracy on test data and supports incremental retraining so the baseline adapts as the network evolves — without requiring a full retrain from scratch.
Outcomes
ZTADS demonstrated that a lightweight, ML-driven zero-trust monitor can be deployed on commodity hardware with minimal overhead. Detection latency averaged 87ms per session, and false-positive rates were kept below 2% through careful feature selection and threshold tuning.
The project sharpened skills across network security, supervised learning, real-time data pipelines, and security-focused UI design — forming the foundation for future work in SOC tooling and threat intelligence automation.